主要步骤: 首先将windows10 iso镜像文件解压到一个文件夹,我们这里解压到C:\WinISO 创建挂载文件夹: mkdir C:\Mount 查看要安装的系统版本的索引: dism /Get-WimInfo /…
CentOS7彻底卸载nvm教程
CentOS7卸载nvm 在 CentOS 7 上卸载 NVM(Node Version Manager)可以通过以下步骤进行。NVM 是一个用于管理多个 Node.js 版本的工具,卸载 NVM 需要删除其安装目录和相…
2025派小星DNS二级域名分发公测免费版
一站式对域名进行二级分发,自助添加,自助修改解析,支持市面上所有主流DNS产商,卡密功能,多用户组,用户组单独设置可解析域名和解析价格,工单功能,支持易支付接口和聚合登录接口。 1.程序必须使用PHP8.1 2.将扩展i…
手动提供 PO Token(用于 web 客户端)
本节提供了在网页浏览器中从 YouTube 手动提取 PO Token 的基本指南,**用于 **web 客户端,并通过 po_token 提取器参数手动传递给 yt-dlp。这种 PO Token 提取方法可能也适用于…
centoss7端口转发规则
# 开启 IP 转发 echo 1 > /proc/sys/net/ipv4/ip_forward # 添加永久性 IP 转发配置 echo "net.ipv4.ip_forward = 1" …
Sphinx 搜索引擎管理脚本使用说明
脚本概述 sphinx_manage.sh 是一个用于管理多个 Sphinx 搜索引擎实例的 Shell 脚本。该脚本可以同时管理多个 Sphinx 配置文件,支持启动、停止、重启、重建索引和查看状态等基本操作。 环境要…
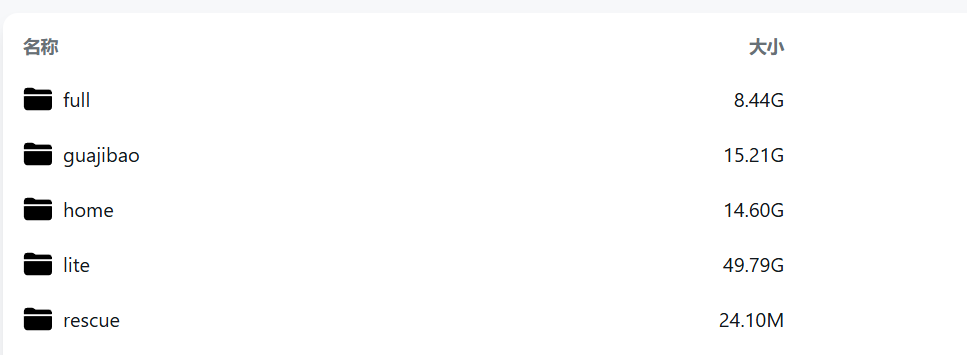
nat.ee Windows精简包
Windows精简包 https://prod-vod.miyoushe.com/1b84fc6046e44ebb861a4abcedd7e738.tar.gz
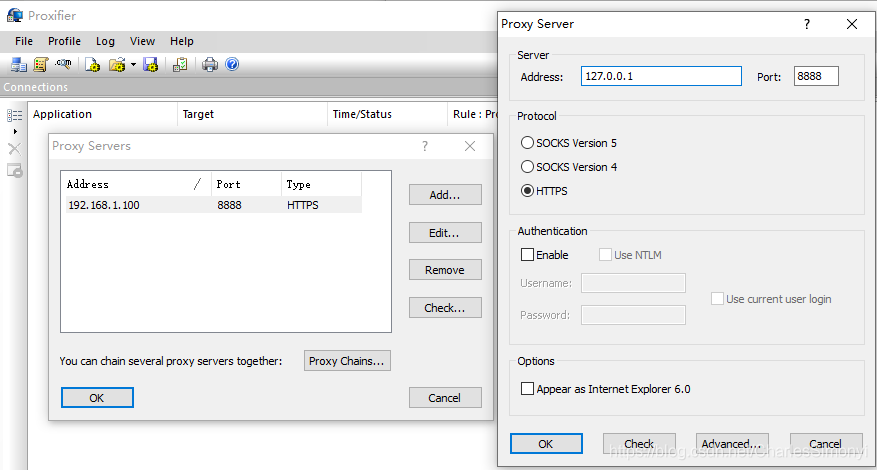
Proxifier抓包设置
强行设置代理 既然它不支持设置代理,我们就借助其它软件给它设置代理,比如: Proxifier: https://www.proxifier.com SocksCap64:https://www.sockscap64.c…
从浏览器手动获取 PO Token
此过程通过在网络浏览器中手动获取在 YouTube 上生成的 PO 令牌,然后通过po_token提取器参数手动将其传递给 yt-dlp。 步骤: 在浏览器中 打开YouTube Music或 YouTube Embed…